
SSH and Telnet are both network protocols made for managing and gaining access to remote computers. When should we choose one over the other and how do they differ from one another? In this post, we’ll compare Telnet with SSH and discuss the pros and cons of each. Before delving into the specifics of Telnet vs. SSH, it is important to understand both protocols better.
Describe Telnet.
Terminal Network, or “Telnet,” is a term that is almost as old as the internet. The common TCP/IP protocol called Telnet was created for virtual terminal services. You can connect to a remote system in a way that makes it seem like a local system by using Telnet. Telnet is a network protocol that permits virtual computer access and offers two-way, group text-based communication between two systems.

Describe SSH.
A network protocol called SSH (Secure Shell), commonly referred to as Secure Socket Shell, gives users, particularly system administrators, a secure way to access a computer across an unprotected network. You can use SSH to encrypt data transmissions between two computers connected over an open network in addition to robust password and public key authentication. Simply put, the SSH protocol can encrypt traffic going both ways, assisting you in avoiding problems like trafficking, sniffing, password theft, and others.
SSH is also commonly used by network administrators to remotely manage a variety of systems and applications. Network administrators can use this SSH functionality to connect in to another computer remotely, run commands, and transfer files between computers. Knowing these protocols now will help us in the section that follows when we talk about the comparison between Telnet and SSH.

What are the primary distinctions between SSH and Telnet?
Even though Telnet and SSH share certain similarities, both protocols can be distinguished by their significant differences. SSH is more secure than Telnet, which is the main difference between the two. Because of this, we may assert that SSH has largely replaced Telnet in all services. In light of this, let’s compare Telnet and SSH in more depth.
Telnet and SSH comparison:
Even their definitions differ when Telnet and SSH are compared. The networking protocol known as Telnet, which stands for Telecommunications and Networks, is mostly used on the UNIX operating system. SSH, or Secure Shell, is a cryptographic network protocol that allows for the secure operation of network services across an unprotected network. SSH let you transfer files between systems, log into a distant computer over a network, and run commands on that computer.
To handle the distant system using Telnet, a server programme must be installed on it. Additionally, the client application needs to be installed on the local PC. TCP protocol and port 23 are utilised to make it feasible for you to connect to a remote machine via Telnet. After that, this machine can receive commands and perform the role of a Telnet server. Commands are sent using the NVT (Network Virtual Terminal) format. The server will then take these commands in, interpret them, and send them to the correct application.
Operation: Telnet vs. SSH
To handle the distant system using Telnet, a server programme must be installed on it. Additionally, the client application needs to be installed on the local PC. TCP protocol and port 23 are utilised to make it feasible for you to connect to a remote machine via Telnet. After that, this machine can receive commands and perform the role of a Telnet server. Commands are sent using the NVT (Network Virtual Terminal) format. The server will then take these commands in, interpret them, and send them to the correct application.
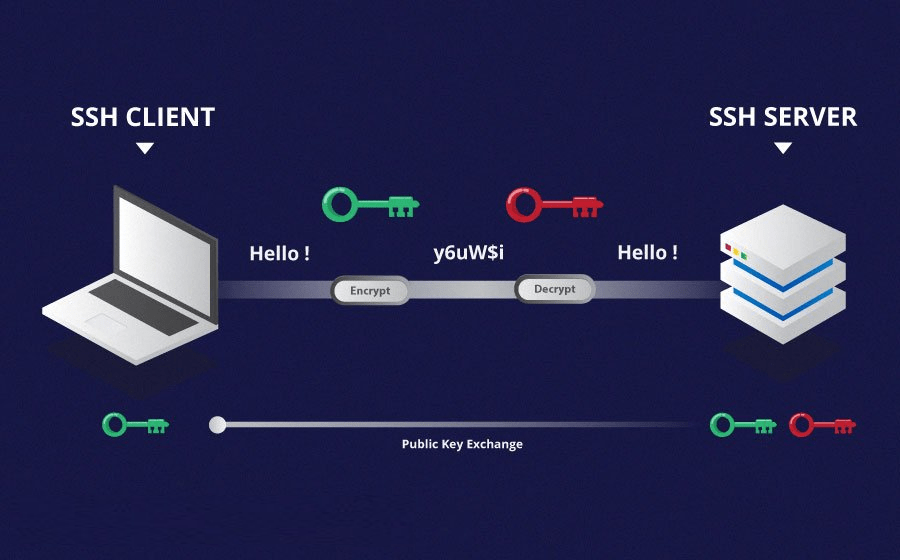
SSH, on the other hand, uses port 22 to give you a secure connection to the server (note that you can change the port number). Since SSH employs key-based authentication, as you may be aware, a session key is generated and delivered to both the client and the server after the client has verified the server. This key encrypts the session’s traffic. The client authentication procedure is concluded by the server authenticating the client using a produced SSH key pair. We created an encrypted connection by following these procedures, allowing the two systems to safely share data.
SSH vs. Telnet: Security
Telnet is quite insecure because it doesn’t employ any security procedures when transferring data. Therefore, it is dangerous to use this protocol unless we use Telnet on private and trusted networks. The opposite is true with SSH sessions, which use paired keys for authentication. As you may imagine, this method makes it very difficult to decode and read the transmitted data. SSH is therefore regarded as a very secure method of sending data over insecure networks.
Authentication in Telnet vs. SSH
Telnet provides no methods for connection establishment that need authentication. However, the most popular and secure SSH authentication method used by SSH is public-key encryption. The client holds the private key after the creation of the SSH key pair. The public key is transmitted to a server in the interim. When a client wants to connect to a server using SSH, the server verifies the client’s identity by comparing the client’s public and private keys. Two systems can link securely if their keys are same.
SSH vs. Telnet: Data Format
Using the Network Virtual Terminal format, Telnet can only send data in plain text; in contrast, SSH can encrypt information going both ways. SSH uses a secure channel in addition to an encrypted format for data transmission.
Use cases of SSH vs. Telnet
SSH is useful for practically all use cases and is especially beneficial for public networks because it is far more secure than Telnet. SSH provides more features, such as secure file transmission and port forwarding, than Telnet. However, in the following two circumstances, Telnet is advised over SSH:
- You can use Telnet to access secure, private networks, such LANs.
- When utilising non-SSH capable devices
Telnet’s lack of security is no longer a problem under these circumstances, and the reduced bandwidth utilisation is also advantageous. In this part, we compared Telnet and SSH from several perspectives. You will become familiar with their key benefits and drawbacks in the paragraph that follows.
What benefits and drawbacks does Telnet offer?
We’ve listed some of Telnet’s advantages and disadvantages below.
Advantages of Telnet
- The Telnet protocol can be helpful for trouble-free information sending and receiving.
- A network virtual terminal is implemented by all terminal network clients and servers (NVT).
- Almost all types of operating systems support Telnet.
- This protocol can save a lot of time because you don’t need to physically visit any hosts.
- Telnet is incredibly adaptable, so you can easily install it on any system.
Negative aspects of Telnet
- Security hazards might result from unencrypted data transmission using Telnet.
- Given that Telnet is a character-based communication method, GUI-based tools cannot be used through Telnet connections. Additionally, it is not possible to send mouse movements or other GUI data.
- Because Telnet is not secure, hackers can access information like usernames and passwords.

Telnet can have several weaknesses, as we discussed in this part, so Secure Shell was developed in the middle of the 1990s to ensure safety and security.
What SSH benefits and drawbacks are there?
Of course, SSH is more secure than Telnet; However, SSH has its pros and cons.
Advantages of SSH
Data encryption is possible using SSH, preventing hackers and attackers from accessing user data and passwords. SSH additionally enables the tunnelling of other protocols, such as FTP. The following are some of the issues that SSH can shield you from:
- Source-routing IP
Source routing frequently serves beneficial reasons, such as changing a network signal’s path. However, if it doesn’t work, it might also be tricked by malevolent users, leading a system to believe it is speaking to a different machine.
- DNS Spoofing
In a hacking operation known as DNS spoofing, malicious Domain Name System data is inserted into the server’s cache database. By returning an inaccurate IP address as a result of this DNS cache poisoning, the name server sends traffic to a different machine. Attackers have access to sensitive data through their computers.
- Manipulating data
The attacker can collect or alter data at intermediaries along with the network route. This problem frequently happens at routers, which act as a form of gateway or checkpoint for data travelling to their destination.
- Sniffing or listening to sent data
An attacker can monitor your data and gather any private or sensitive information if you are using an unprotected connection for their malevolent purposes.
- IP address forgery
Making Internet Protocol (IP) packets with a bogus source IP address is known as IP address spoofing. The source’s location and identity are concealed in this manner, allowing the attacker to mimic them by using a different computing machine.
Disadvantages of SSH
- Added preparation time compared to Telnet.
- SSH lacks a built-in GUI.
- SSH usage calls for additional technical expertise.
You can read this post to learn more about the best SSH client for Windows after reading the comparison between Telnet and SSH. You might have another query in mind. How can we set up a line on a terminal server or router?
What is Telnet transport input SSH?
You can remote access devices via the virtual terminal (VTY) lines. You can select which protocols are permitted access to the virtual terminal lines using the Cisco “transport input” command. The following transport input command keywords will allow you to set the permitted protocols on the VTY lines.
- ssh: allows TCP/IP SSH protocol only
- telnet: allows TCP/IP Telnet protocol only
- all: allows all protocols
- none: blocks all protocols
- telnet ssh: allows both Telnet and SSH protocols
Additional Telnet commands
This list includes some of the Telnet commands:
- Open-To connect to a host using Telnet, open the port specified by the hostname.
- Close-aids in terminating an active Telnet connection
- Quit: to exit from Telnet
- Status-figuring out whether or not the Telnet client is connected.
- Timing Mark– Describes timing Mark
- Terminal Type/Speed: Setting the terminal type and speed
Other SSH Commands
Here are some useful SSH commands:
- Is-Display the directory’s content
- Cd-assisting with directory change
- mkdir-you make a brand-new folder (directory)
- touch-letting you delete a file.
In today’s IT and DevOps businesses, remote connections to server infrastructure are commonplace. But there are a few good options to take into account when selecting an authentication protocol. The Windows Remote Desktop Protocol (RDP) and SSH are two protocols that come to mind.
This article’s earlier sections compared Telnet and SSH from a variety of angles. Here is a comparison between RDP and SSH so that you can make an informed decision. But first, do you know what RDP is before we compare these two protocols?
Describe RDP.
Only physical Windows servers and Windows virtual machines (VMs) can be accessed using the Remote Desktop Protocol. RDP may give you, the user, a Windows Graphical User Interface (GUI) experience, which increases the usability of servers for many workers, even if they lack technical knowledge. In this respect, we take pride in being able to provide our clients with the most dependable, high-performance RDP servers, with a 99.95% uptime. By clicking the link below, you can compare the top RDP Servers with ease.
Conclusion
Telnet and SSH are two network protocols that can be used to remotely access and control devices. Telnet is still helpful in some circumstances, even if SSH protocol is the superior choice. It’s crucial to keep in mind that the primary distinction between SSH and Telnet is that SSH encrypts all data, including usernames and passwords, throughout travel in both ways. Additionally, purchasing RDP is an option if you prefer a GUI experience. When using RDP, you can connect to another computer via a network using a graphical interface.
FAQ
Why was Telnet replaced by SSH?
Telnet has a secure substitute in SSH. This protocol can defend against eavesdropping attempts and secure user identities, passwords, and data.
Is Telnet a threat to security?
Telnet submissions of credentials (usernames and passwords) are not secured, leaving them susceptible to identity theft.
Is Telnet a security risk?
Telnet submissions of credentials (usernames and passwords) are not secured, leaving them susceptible to identity theft.
Is SSH faster than Telnet?
Since there is no key exchange or encryption, the Telnet protocol is quicker.
What distinguishes SSH and RDP from one another?
Both can be used to connect remotely to computers and other servers, but RDP’s GUI design makes it more user-friendly for non-technical staff members.
Read Our Next Articles In 2023 ,The top 10 SSH clients

